Reflected Cross-Site Scripting (XSS) Vulnerability in Contact Form 7 – Dynamic Text Extension
While working on a security review of a WordPress plugin today we wanted to get a better idea if part of how the plugin is handling something was common, despite seeming problematic from a security standpoint. When we did a search using WPdirectory we saw it was a very common practice, but also with one of the most popular plugins flagged we saw what seemed to like a fairly obvious security vulnerability unconnected to that. A quick check confirmed that the plugin, Contact Form 7 – Dynamic Text Extension, which has 100,000+ installs, has a reflected cross-site scripting (XSS) vulnerability. That isn’t a very serious vulnerability, but is something that seems like it should have been noticed considering that you don’t have to go any farther that the description of the plugin to see an indication that it might exist.
The plugin registers the shortcode “CF7_GET” to cause the function cf7_get() to run:
288 | add_shortcode('CF7_GET', 'cf7_get'); |
That function will output user input in the form of a GET input without sanitizing or escaping it, which is a reflected XSS vulnerability:
278 279 280 281 282 283 284 285 286 287 | function cf7_get($atts){ extract(shortcode_atts(array( 'key' => 0, ), $atts)); $value = ''; if( isset( $_GET[$key] ) ){ $value = urldecode($_GET[$key]); } return $value; } |
While it is unrelated to the vulnerability, the documentation for the function it is passed through urldecode() warns against doing what is done there:
WarningThe superglobals $_GET and $_REQUEST are already decoded. Using urldecode() on an element in $_GET or $_REQUEST could have unexpected and dangerous results.
It looks like there are additional issues with lack of proper sanitization/escaping in the plugin.
Full Disclosure
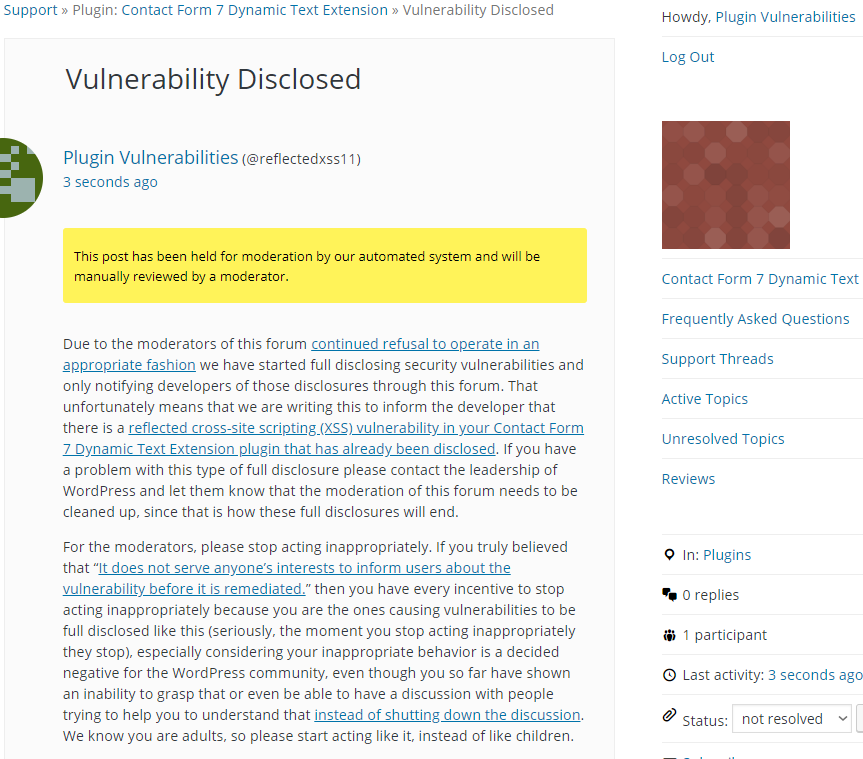
Due to the moderators of the WordPress Support Forum’s continued inappropriate behavior we are full disclosing vulnerabilities in protest until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. You can notify the developer of this issue on the forum as well. Hopefully the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information, can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof of concept will cause the number “1” to be shown in an alert box. Major web browsers other than Firefox provide XSS filtering, so this proof of concept will not work in those web browsers.
Make sure to replace “[path to shortcode]” with the location of a page with the shortcode “CF7_GET”.
http://[path to shortcode]/?0="><script>alert(1);</script>
Thanks for pointing this out – a fix has been released (July 24, 2019, v 2.0.3).
While this should indeed be fixed, it should be noted that this would only affect users who are using the shortcodes outside of the prescribed usage (which is within a Contact Form 7 Form Tag). When used as prescribed (as form tag default values), the values are escaped before being added as attribute strings to the input tags, which protects from this attack. So fortunately the real-world impact of this vulnerability should be minimal, as there’s really no reason for a user to place the shortcode outside of a CF7 form tag.
We’ve published a disclosure with more details here: https://sevenspark.com/docs/cf7-dtx-security-2019-07-24
Thanks!