Automattic Has a lot of Work to do on the Security of the Zero BS WordPress CRM Plugin
A couple of months ago we discussed Automattic’s concern or lack thereof for the security of WordPress plugins in the context of them causing an insecure plugin from Facebook to be installed on websites using their WooCommerce plugin. A week ago it was announced they had purchased the plugin Zero BS WordPress CRM. After seeing that we started to take a quick look over the security of the plugin, but we didn’t get far in to that before finding the plugin has some obvious security issues.
As one quick example of the insecurity, we found that someone that could get a logged in Administrator to click a link, say one left in a comment on the website, could cause all of the plugin’s data to be deleted, which is pretty big issue for a CRM plugin. So it would appear that Automattic didn’t do security due diligence of the plugin before the purchase, considering if they had, they should have reported the issues to the developer and they should have been fixed by now.
Automattic’s continued lack of concern for the security of plugins is problematic as the head of Automattic is also the only person that appears to have oversight of the team running the Plugin Directory, a team that seems to be disinterested in the security of plugins at best.
Details
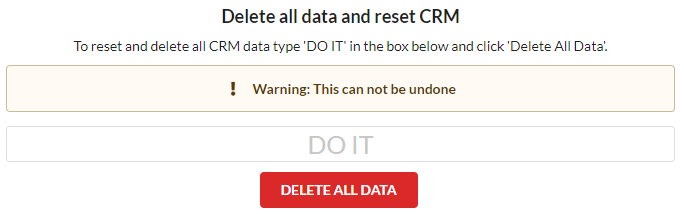
If you intentionally try to delete all the plugin’s data you have to go through a two step process where you first have to enter a phrase:
Then you have confirm you really want to do that:
The other way that could be done is by simply going to this URL:
/wp-admin/admin.php?page=zerobscrm-datatools&zbs-delete-data=1
What is missing from the URL is a nonce, which is used to prevent unintentional actions from being taken, in this case, deleting all of the data when you just click on a link. That is referred to as cross-site request forgery (CSRF).
Looking at the underlying code provides more concern about the quality of the code in the plugin as we found that one of the files involved in that has an unused duplicate. Access to the admin page being access when visiting that URL is defined in both the file /includes/ZeroBSCRM.Core.Menus.php and /includes/ZeroBSCRM.Core.Menus.WP.php. The former doesn’t look to be actually being used anywhere in the plugin. In the latter the Data Tools admin page is restricted to users with the “admin_zerobs_manage_options” capability:
132 | $adminMenuData = add_menu_page( __('Data Tools',"zero-bs-crm"), __('Data Tools',"zero-bs-crm"), 'admin_zerobs_manage_options', $zbs->slugs['datatools'], 'zeroBSCRM_pages_datatools', 'dashicons-admin-tools',90); add_action( "admin_print_styles-{$adminMenuData}", 'zeroBSCRM_global_admin_styles' ); |
Accessing that page calls the function zeroBSCRM_pages_datatools() which again checks for that capability and then runs the function zeroBSCRM_html_datatools():
3429 3430 3431 3432 3433 3434 3435 3436 | function zeroBSCRM_pages_datatools() { global $wpdb, $zbs; if (!current_user_can('admin_zerobs_manage_options')) { wp_die( __('You do not have sufficient permissions to access this page.',"zero-bs-crm") ); } zeroBSCRM_pages_header('Import Tools'); zeroBSCRM_html_datatools(); |
Confusingly that function checks for a different capability before permitting the data reset to happen through the function zeroBSCRM_database_reset():
3917 3918 3919 3920 3921 3922 3923 3924 3925 | function zeroBSCRM_html_datatools(){ global $wpdb, $zbs; $deleting_data = false; if(current_user_can('manage_options')){ if ( isset($_POST['zbs-delete-data']) && $_POST['zbs-delete-data'] == 'DO IT'){ |
3944 3945 3946 | } else if ( isset( $_GET['zbs-delete-data'] ) && $_GET['zbs-delete-data'] == 1){ zeroBSCRM_database_reset(); |
That function does the same capability check, but like the other code doesn’t check for a valid nonce:
528 529 530 | function zeroBSCRM_database_reset(){ if(current_user_can('manage_options')){ |
Full Disclosure
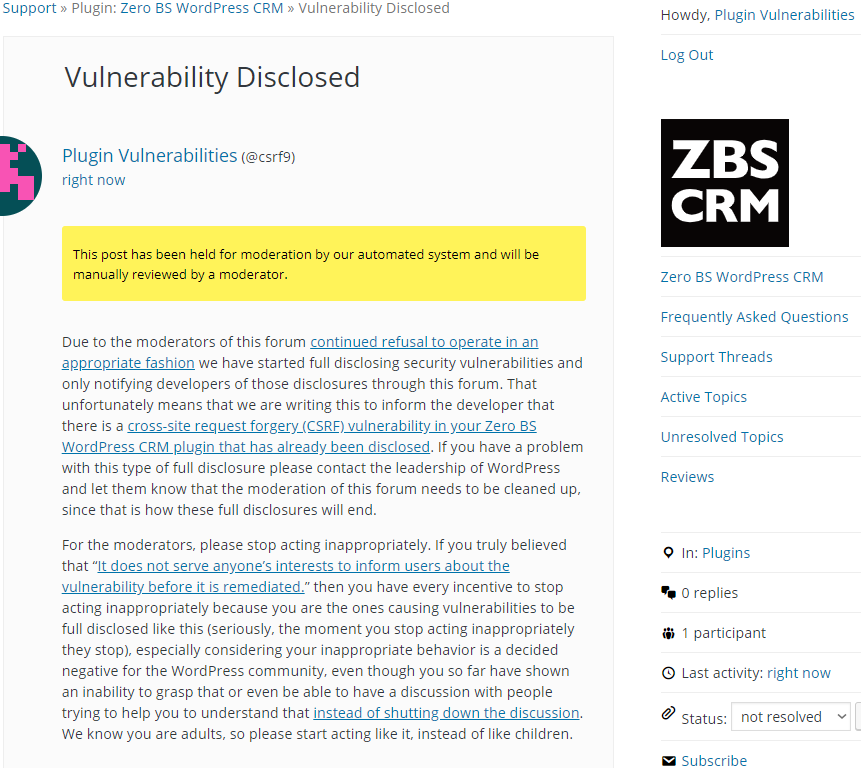
Due to the moderators of the WordPress Support Forum’s continued inappropriate behavior we are full disclosing vulnerabilities in protest until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. You can notify the developer of this issue on the forum as well. Hopefully the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information, can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof of concept will reset the plugin’s data, when logged in as an Administrator.
Make sure to replace “[path to WordPress]” with the location of WordPress.
http://[path to WordPress]/wp-admin/admin.php?page=zerobscrm-datatools&zbs-delete-data=1