Five of the 100 Most Popular WordPress Plugins Are Insecurely Using the extract() Function
Last week we noted that the most popular WordPress security plugin, Jetpack, was insecurely using PHP’s extract() function. It turns out that it isn’t alone among the most popular WordPress plugins, as running the 100 most popular plugins in the WordPress Plugin Directory through our Plugin Security Checker identified four more plugins that are similarly insecure. Jetpack is the most popular with 5+ million installs according to WordPress’ stats, but the others are also have large install counts:
- Advanced Custom Fields: 2+ Millions Installs
- CookieYes GDPR Cookie Consent & Compliance Notice: 1+ Million Installs
- MetaSlider: 700,000+ Installs
- Ocean Extra: 700,000+ Installs
As we noted in the previous post, the documentation for the extract() function has this warning:
WARNING Do not use extract() on untrusted data, like user input (e.g. $_GET, $_FILES).
The WordPress coding standards go farther and say don’t use that function at all.
But with each of these plugins, they use the function on user input in the form of shortcode attributes. While none of those plugins look to have an obvious vulnerability due directly to the usage of extract(), we have now confirmed that at least one of them, CookieYes GDPR Cookie Consent & Compliance Notice, does contain a vulnerability related to that. It concerning to see a relatively easy to spot vulnerability in a plugin used to deal with the data protection and privacy EU regulation General Data Protection Regulation (GDPR). This is second plugin designed to assist with that, which we have found is insecure this week. The other being one that contains a vulnerability hackers would exploit.
In July, Automattic, through their Jetpack blog, had put out a post about a vulnerability in plugin that involved usage of extract() and they claimed in that “we work hard to make sure your websites are protected from these types of vulnerabilities”. We then contacted Automattic, suggesting that they could help to address the insecure usage of extract() in plugins on a wider scale, as about half of the WordPress security team are employees of that company and that team should be able to get the team running the WordPress Plugin Directory to start addressing this. We haven’t heard back from them and we later realized that one of their own plugins was part of the problem.
Authenticated Persistent Cross-Site Scripting (XSS)
The CookieYes GDPR Cookie Consent & Compliance Notice plugin registers a shortcode, “cookie_audit”, which calls the function cookielawinfo_table_shortcode():
45 | add_shortcode( 'cookie_audit',array($this,'cookielawinfo_table_shortcode')); |
Right at the beginning of the function, which is located in the file /public/modules/shortcode/shortcode.php, the extract() function is used on user input in the form of shortcode attributes:
177 178 179 180 181 182 183 184 185 186 187 188 189 190 | public function cookielawinfo_table_shortcode( $atts ) { /** RICHARDASHBY EDIT: only add CSS if table is being used */ wp_enqueue_style($this->plugin_name.'-table'); /** END EDIT */ extract( shortcode_atts( array( 'style' => 'classic', 'not_shown_message' => '', 'columns' =>'cookie,type,duration,description', 'heading' =>'', 'category'=>'' ), $atts ) ); |
No validation or sanitzation is done when bringing in the user input there, which is a big security risk and part of the issue with using extract(). If, for example, one of those inputs is then output without escaping, that would permit persistent cross-site scripting (XSS) to occur. That is exactly what occurs with the shortcode attribute “style” which is converted to the variable $style:
247 | $ret = '<table class="cookielawinfo-row-cat-table cookielawinfo-' . $style . '"><thead><tr>'; |
That wouldn’t be a vulnerability for WordPress users with the “unfiltered_html” capability as they are allowed to do the equivalent of XSS, but as the proof of concept below confirms, lower-level users without that capability can exploit this.
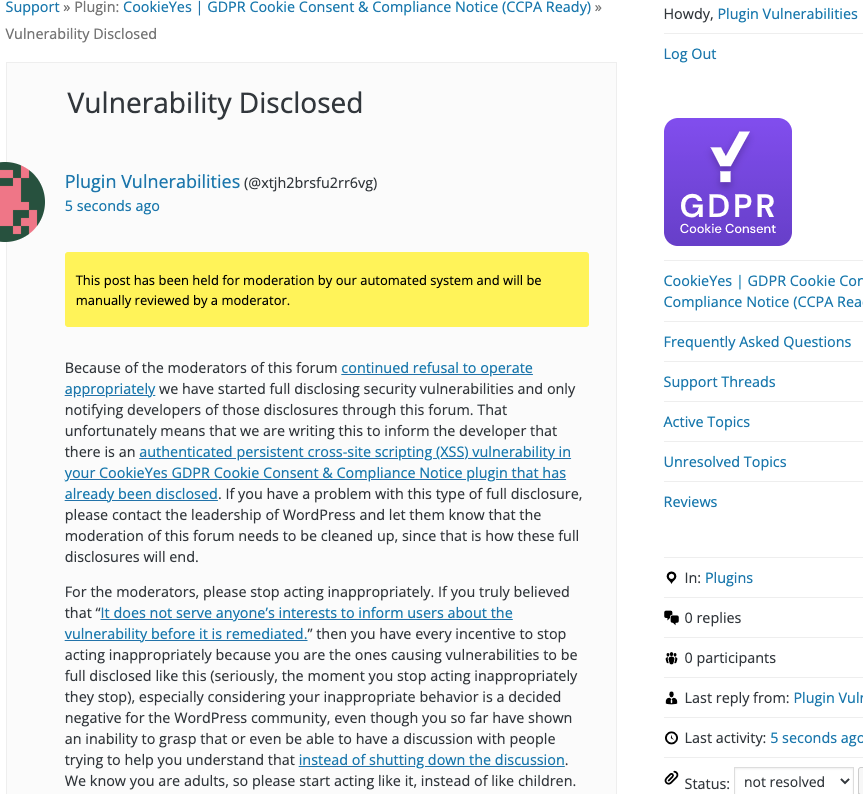
WordPress Causes Full Disclosure
Because of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.) You can notify the developer of this issue on the forum as well. Hopefully, the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
Creating a new post as a user with the Author role, which doesn’t have the unfiltered_html, with the following shortcode will cause an alert box with any available cookies to be shown when hovering over the plugin’s content on the page.
[cookie_audit style=' " onmouseover="alert(document.cookie);']