Despite “Manual Security Review”, Brand New WordPress Plugin Contains Multiple Vulnerabilities
Before new plugins are allowed in to WordPress’ plugin directory, they are claimed to go through a manual review:
After your plugin is manually reviewed, it will either be approved or you will be emailed and asked to provide more information and/or make corrections.
That is supposed to involve a review of the security of the plugin:
You will get an automated email telling you about the submission immediately. At that point, someone will manually download and review your code. If we find no issues with the security, documentation, or presentation, your plugin will be approved. If we determine there are issues, you will receive a second email with details explaining what needs to be fixed.
The head of WordPress, Matt Mullenweg, though, seems to believe those reviews don’t happen, but apparently doesn’t see an issue with claiming they are occurring (the WordPress website claims that one person has somehow reviewed 46,800 plugins).
Either the security reviews are not happening or they are missing things they shouldn’t, as once again our proactive monitoring of changes made to plugins in the Plugin Directory to try to catch serious vulnerabilities caught a variant of a serious security vulnerability in a brand new plugin. We have for years offered to provide the team that is supposed to be doing the reviews, either access to tools we have that warn about such things or help them have the capability themselves, without our offer being taken up or this problem otherwise being addressed.
This time the vulnerability exists in a plugin named PageManager, which has a cross-site request forgery (CSRF)/PHP object injection vulnerability. The same code also permits changing settings through CSRF.
We now are also running all the plugins used by customers through that on a weekly basis to provide additional protection for our customers.
The possibility of this vulnerability is also flagged by our Plugin Security Checker, so you can check plugins you use to see if they might have similar issues with that tool.
We tested and confirmed that our new firewall plugin for WordPress protected against the type of exploitation of this vulnerability you would see in a mass hack, even before we discovered the vulnerability, as part of its protection against zero-day vulnerabilities.
CSRF/PHP Object Injection
The automated portion of the proactive monitoring flagged the following line of code in the plugin:
144 | $settings = unserialize(base64_decode($_POST['settings'])); |
That will pass the base64 decoded version of the POST input “settings” through the unserialize() function, which would permit PHP objection injection to occur, which allows an attacker the ability to get code to run when not intended.
Whether there is a vulnerability would depend on who can access that.
That line of code is in the function importAction(), which is located in the file /pagemanager/src/Controller/IndexController.php:
133 134 135 136 137 138 139 140 141 142 143 144 | public function importAction() { $settings = get_option('pagemanager_settings', []); if (!isset($settings['pagetype'])) { $this->settingsAction(); return $this; } if (isset($_POST['settings'])) { $settingsInst = Settings::getInstance(); $settings = unserialize(base64_decode($_POST['settings'])); |
That function runs when accessing the plugin’s “Import settings” page in WordPress’ admin area, which would only be accessible by Administrators in a standard setup. It wouldn’t be a vulnerability for an Administrator to do the equivalent of PHP object injection. That code doesn’t include a nonce check, so this could be exploited cross-site request forgery (CSRF), with an attacker causing an Administrator to take the action without intending it. That code is intended to handle importing the plugin’s settings, so that is also susceptible to CSRF.
Even without looking at the code, the CSRF issue with settings import should have be spotted in a security review of the plugin.
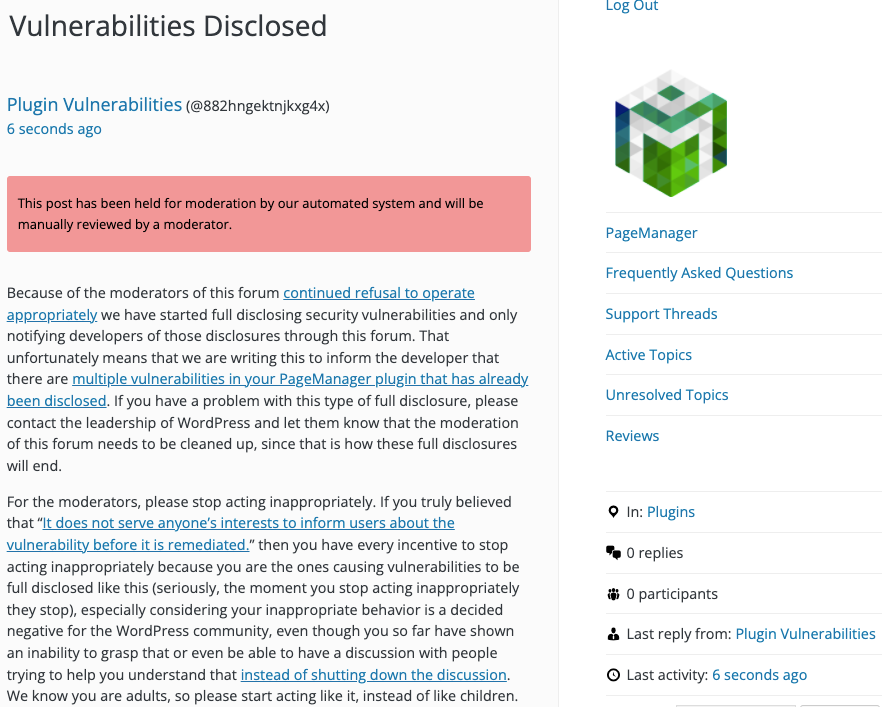
WordPress Causes Full Disclosure
As a protest of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.)
You can notify the developer of this issue on the forum as well.
Hopefully, the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
If the moderation is cleaned up, it would also allow the possibility of being able to use the forum to start discussing fixing the problems caused by the very problematic handling of security by the team running the Plugin Directory, discussions which they have for years shut down through their control of the Support Forum.
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
With our plugin for testing for PHP object injection installed and activated, the following proof of concept will cause the message “PHP object injection has occurred.” be shown, when logged in to WordPress as an Administrator.
Replace “[path to WordPress]” with the location of WordPress.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin.php?page=import_pagemanager" method="POST"> <input type="hidden" name="settings" value="TzoyMDoicGhwX29iamVjdF9pbmplY3Rpb24iOjA6e30=" /> <input type="submit" value="Submit" /> </form> </body> </html>